In the upcoming digest piece, we’ll go over an overview of our Pessimistic Spotter on-chain monitoring & defense service!
-
spotter.pessimistic.io — Sign-up!
-
pessimistic_spotter_public — Public Alerts Channel
Please subscribe to our blog to make sure you don’t miss any of the regular news and updates we plan to publish on the project in a special digest!
So, today we would also like to go through all of our work from September 2021 to April 2023 with you and reflect all of the particularly significant events in one article.
Let’s get it started!
Spotter Starting Up
According to the questions, the audience has several points that need to be discussed further. That’s what we’ll do next!
At the very beginning, it is critical to note that the idea of creating a Web3 version of Web2 security systems (e.g. IDS, SIEM, DLP), specifically from the banking sector, “but on the blockchain” has been floating around in the minds of market participants for a long time, and with the recent increase in high-profile hacks, this need has become apparent.
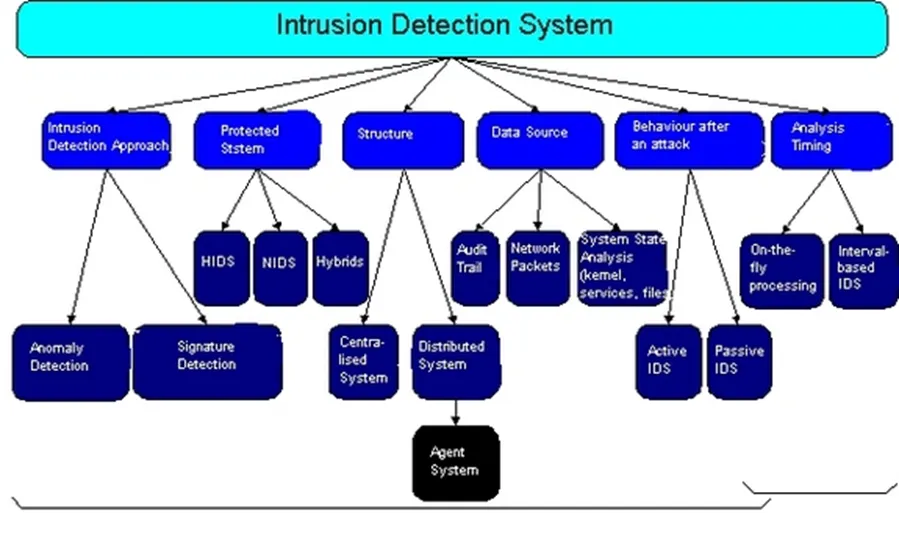
For example, here is the technology I described in 2020, and it is similar to the implementation of roughly the same web2-origin thing (assuming there already was a DLP/IDS/SIEM system) but in blockchain:
Hacks began to threaten our entire market, and as experience has shown, in order to protect yourself reliably, you must be one step ahead of the hacker, so we devised the concept of monitoring and active defense for both blockchain-based projects and their users!

But for us, it all started with the following article; read it to understand what is going on now and to see how and why our project vision was corrected a bit:
Even then, we realized that we needed to take a comprehensive approach, both in terms of monitoring and of applying AI and ML to learn from previous hacks and attacks.
At the same time, it was discovered that there are many options for maneuvering on the side of active protection (important to note — we plan to do this in the future for clients only), ranging from using MEV bots to pausing a smart contract or automatic evacuation of the user’s position from the protocol.
Idea Evolution
We intend to use our system to safeguard both the project and the users, and we will take this very seriously in order to avoid negative scenarios such as False Positive results:
-
Each of the previously described stages has its own set of issues. For example, we will not store users’ private keys (to remove their position from the protocol in case of a hack), but will only store output signatures;
-
Speaking of the protocol/project/contract side, we are going to construct an entire system of active defense on the protocol team side so that we do not become a tidbit target for hackers (and thus become a point of failure in the security system), and to prevent abusing and manipulating our tool and service or with its assistance;
-
It is also very important for us to be able to “catch” the hacker on things that are not quite obvious — for example, by tracing the origin of funds (cluster) that usually finance the deployment of the attacker’s smart contract and so on. If an address is funded from places such as fixedloat, tornado cash and then a smart contract is created, we want to instantly get the information about it. For this purpose, we use various clustering and AML tools, as well as analyze the bytecode and decompile the hacker’s smart contract and the corresponding attacking transactions.
In other words, there are many important nuances on both the user’s and the project’s sides, but the most important aspect of all is reliable and fast monitoring with a low level of false positive and false negative results.
Read our next article, in which we began to reveal exactly what we discussed above, and it finally reflected the project Spotter’s final vision:
Since then, Spotter has been running in public mode; and you can see what transactions it outputs to the result. We believe this beta will be of interest to both protocol and security researchers, please, follow:
Alert Cases
As you probably already know, the whole DeFi industry was very painfully hit by the recent hack of the Euler protocol.
The incident left the protocol devastated and led to a chain of damage to the entire Lego-based DeFi ecosystem. Glad to state that we were able to detect this certain attack on Euler Finance before the attack actually happened:
More successful alerts to date (not to mention numerous successful back-tests alerts):
Next, on March 20th, a series of transactions involving the Ndxfi DEGEN token resulted in an attacker profit of approximately 110 ETH!
Our Spotter system again detected this attack before it actually happened!
The system successfully operated and took action very quickly (it recognized an attack and thus performed the first step — detection), demonstrating once more that it is possible to then pause contracts, launch counterattacks, and take other actions when connecting the experimental part of the Spotter to the supported project.
In other words, our system is in an experimental mode, and the test indicated that we would have enough time to respond!
We could take at least three different approaches to counteract this attack, assuming that it would occur to the supported protocol in the same way that it did to Ndxfi (on a public pool):
-
Сounter-attack hacker via MEV bots (since this exact attack was performed on a public pool) land then return the money to the project.
-
Put the contract on hold (pause) through the integration with the project. Alternatively, it is also possible to set limits or/and pause certain functions only. Check out this article to know more about operational changes in live contracts.
-
And finally, to slow down the attack through the connection with the validators and offer the hacker a bounty beforehand (read more about it here) via RPC pop-ups.
It is important to mention that currently our system does not counter-attack(and does monitoring only) as we first need to sign a contract with the protocol.
Nevertheless, we have confirmed the theoretical possibility of active protection and will continue our research in this direction:
There are more specific things in our distant plans:
-
For example, if the Health Factor of the certain collateral changes (for lending protocols — examples);
-
…or if the protocol you are using is hacked (that’s a custom thing), it can alert the active protection system located either on your own or on our server (and built under our control), which will then make an emergency withdrawal and save your position/assets.
Read more about them in the following digest article, check it out:
Latest News
During the latest Yearn exploit, Spotter again operated successfully and took action very quickly:
We also evolved from the traditional idea of mempool monitoring to include on-chain simulation of events and on-chain fuzzing, ML and AI algorithms — we will gradually apply all of that, but for the time being, we are focusing on making the system multifunctional (almost dual-purpose), safe, and user-friendly.
We must focus our efforts in the near future on “stoichiometric” tasks of this nature! Stay tuned and sign up!
Future Plans
In the near future, we intend to pitch Spotter at a significant number of conferences and turn on protection for a couple of our cordial DeFi protocols. Check out the presentation of the Spotter by our CEO Alexander at the ETHDubai:
This year promises to be full with exciting events! Subscribe to our official resources so you don’t miss anything important:
-
spotter.pessimistic.io — Sign-up!
-
pessimistic_spotter_public — Spotter Public Alerts Channel (Telegram)
-
twitter.com/sadspotter — Follow us on Twitter!
We also ask for your help because we believe that this market is essential, first and foremost for the stability of our sector! Additionally, we have a lot of work to do and are conducting some research concurrently.
As an illustration, we recently released our own customized detectors for a Slither tool:
Please subscribe to our blog to make sure you don’t miss any of the regular news and updates we plan to publish on the project in a special digest!
This almanac, as we said at the beginning, brings together our work over quite an impressive period of time (from September 2021 to April 2023) and if you are confused by the endless stream of news, I hope your path has become a little clearer thanks to this article!
Stay Safe!
Support is very important to me, with it I can do what I love — educating users!
If you want to support my work, please consider donating me to the address:
-
0xB25C5E8fA1E53eEb9bE3421C59F6A66B786ED77A or officercia.eth — ETH, BSC, Polygon, Optimism, Zk, Fantom, etc
-
4AhpUrDtfVSWZMJcRMJkZoPwDSdVG6puYBE3ajQABQo6T533cVvx5vJRc5fX7sktJe67mXu1CcDmr7orn1CrGrqsT3ptfds — Monero XMR